Of Corporate Data Is Now Stored On The Cloud
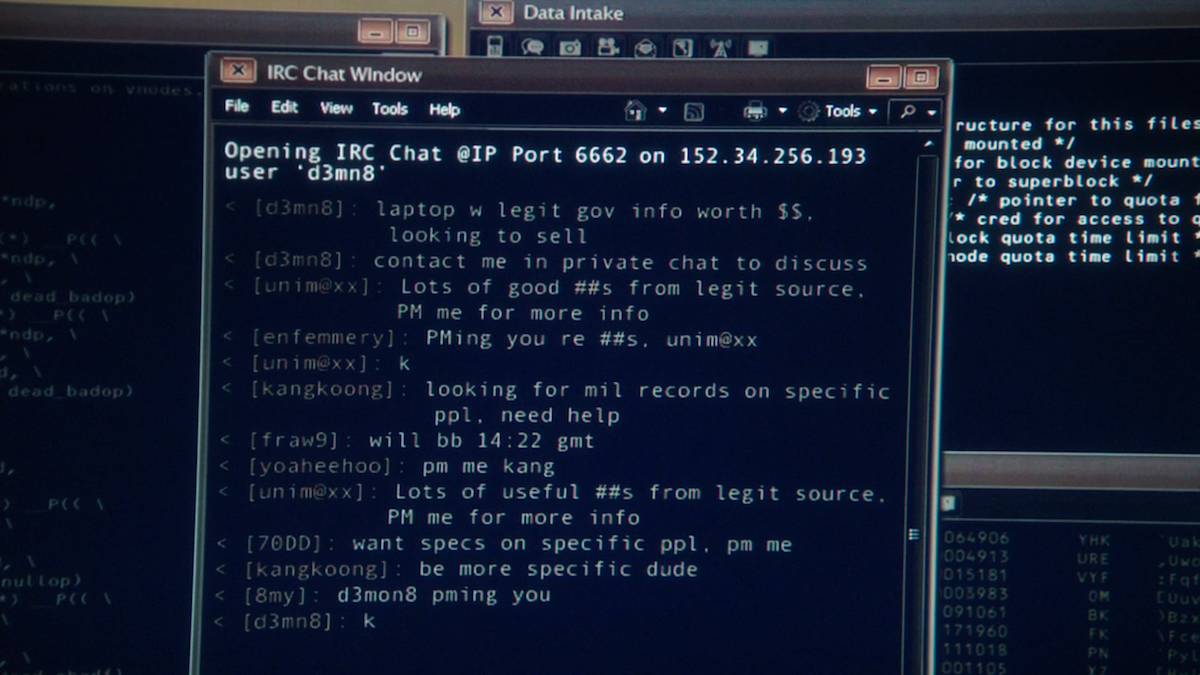
Today, over sixty five,000 unique URLs ending with .onion exist on the Tor network. These useful roles, particularly associated to communication, help many uses which might be thought of legal and legitimate in free societies.
Animals are reportedly tortured, sexually assaulted and killed for the amusement of darknet sadists. Urban legend has it that darknet ghouls view live coverage of murders or hire real-life hitmen to commit homicide.
Artificial Intelligence space has been quickly superior across the international firms corresponding to Google, Amazon, IBM and so on. In addition, it’s anticipated to facilitate the innovation in a wide range of industries in the future.
It has some benefits and helpful functions in addition to drawbacks and vulnerabilities. Tor is in some ways less safe than VPN, but using Tor with VPN can present anonymity and privateness on the internet. I really don’t have anything to cover, however I read a lot about Tor browser, darknet, I am simply curious.
- For example, educational databases are solely out there to college and students, and corporate networks are solely available to employees.
- Peer-to-peer networks and self-hosted web sites are additionally part of the darknet.
- Sites right here usually are not indexed by search engines like google and yahoo as a result of they are merely not accessible to them.
Encryption And The Dark Net
Instead, NordVPN can route your site visitors by way of certainly one of its secure VPN servers after which directly to the Tor network. The NordVPN service can protect all the visitors in your gadget, not just your browser activity как зайти на сайт гидра через тор. With this methodology, you connect with your VPN first and then access the Tor network. There are a few advantages to this methodology, starting with the truth that it’s very straightforward.
Search the world’s largest dataset of darknet content safely from your browser with DarkOwl Vision’s User Interface. Use keywords, search pods, filters, and our personal Lexicon reference software to search out what issues most. There are serious privateness and security issues associated with Network Telescope datasets. Because some viruses and worms contain the installation of backdoors that present unfettered access to contaminated computers, telescope data might inadvertently advertise these weak machines.
Darknet Reddit Makes Search Engine For Darknet Markets
Authentication vector is designed to insert the encrypted knowledge as variable according to the change of time. The security perform was performed by comparing coordinate distance values throughout the authentication vector, and the interior construction was verified to optimize the performance value required for information reverse search. The Darknet and Bitcoins have been extensively utilized by those that want to anonymously carry out unlawful actions in our on-line world. Restricted in many international locations, playing web sites utilize Bitcoin payments that allow users to freely engage in unlawful playing activities with the absence of a formal capable guardian. Despite the urgency and limited information obtainable to law enforcement concerning this concern, few empirical studies have centered on unlawful playing web sites.
